AppVentiX 5 brings powerful enhancements across User Workspace Control, App-V and MSIX deployment, scalability, and administration. Benefit from a more streamlined management experience across your entire environment. Below you’ll find the key highlights of this release, followed by screenshots that provide a closer look at the new capabilities in action.
👤 User Workspace Control
Manage User Workspace Settings
Easily configure and deploy user workspace settings from the AppVentiX Central View console, including:
- Drive mappings
- Printer mappings
- Environment variables
- Group Policies
- Registry keys
- File actions (copy, remove, modify)
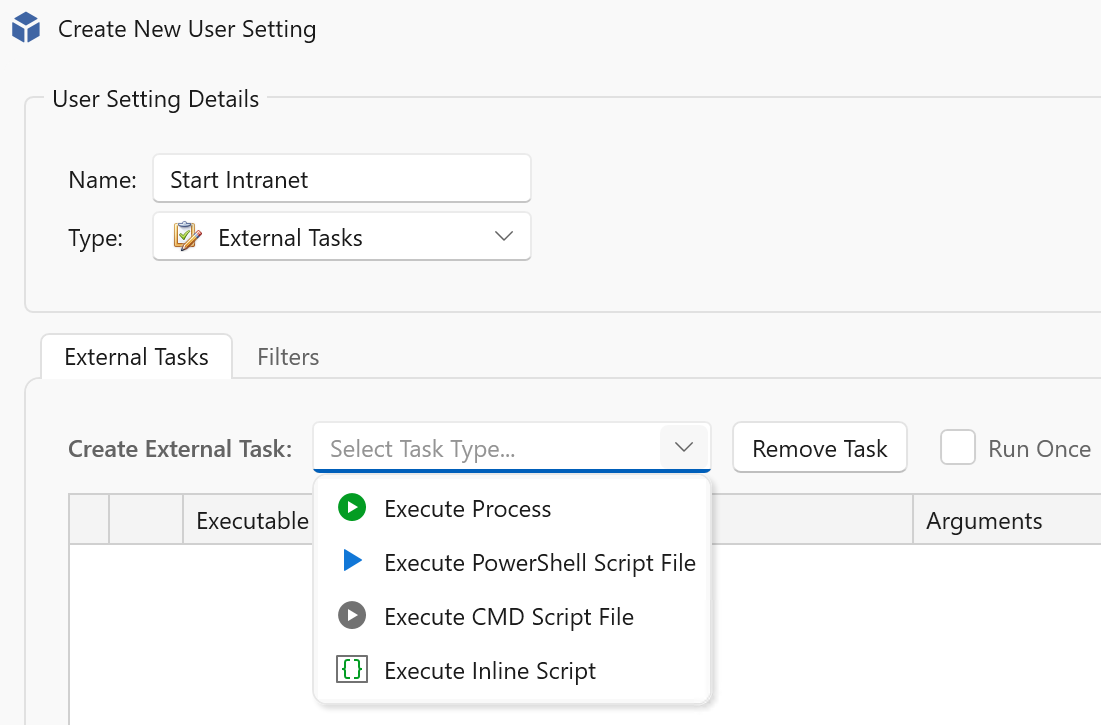
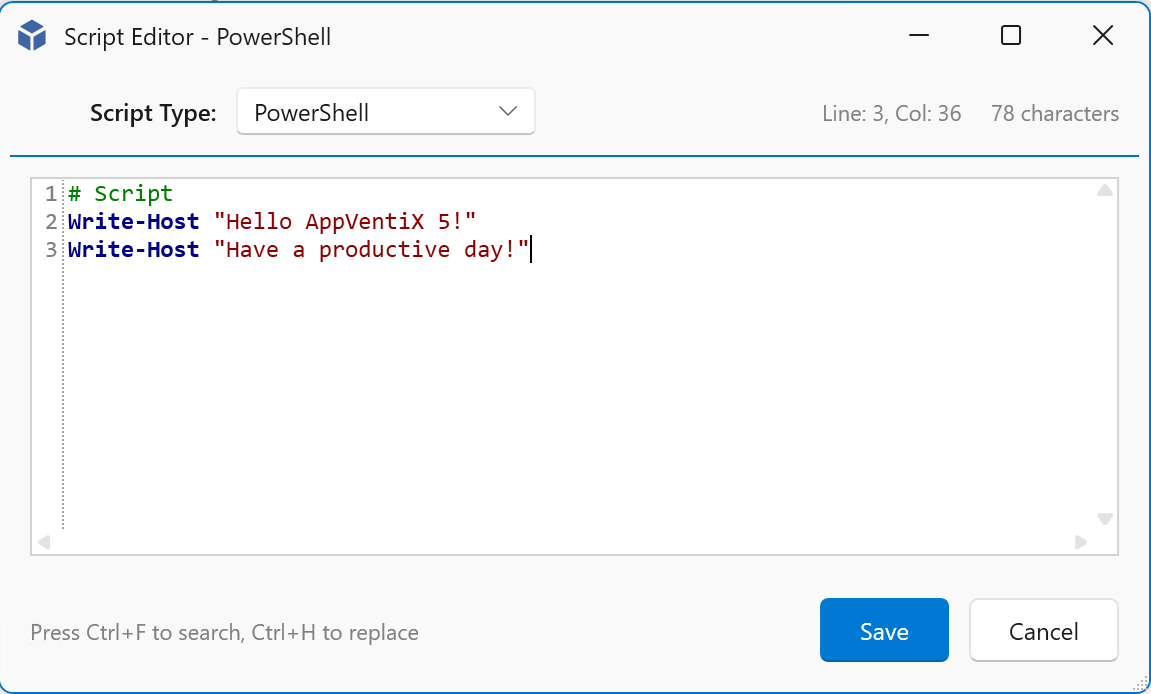
- External tasks including scripts with an embedded script editor
This enables full control over the user workspace without the need for complex scripting or multiple tools. The feature integrates seamlessly with our App-V and MSIX application delivery capabilities.
Login Experience Improvements
- New (optional) progress window at login for better visibility during session initialization
- New Workspace Refresh shortcut for instant refresh of applications and settings
🔐 Security & Compliance
Microsoft App Control for Business Integration
Only allow organization-approved applications and processes, and block everything else to enhance security. The App Control management features include:
- Centralized event monitoring
- Direct policy creation from captured events
- Learning mode for faster, easier policy baselining
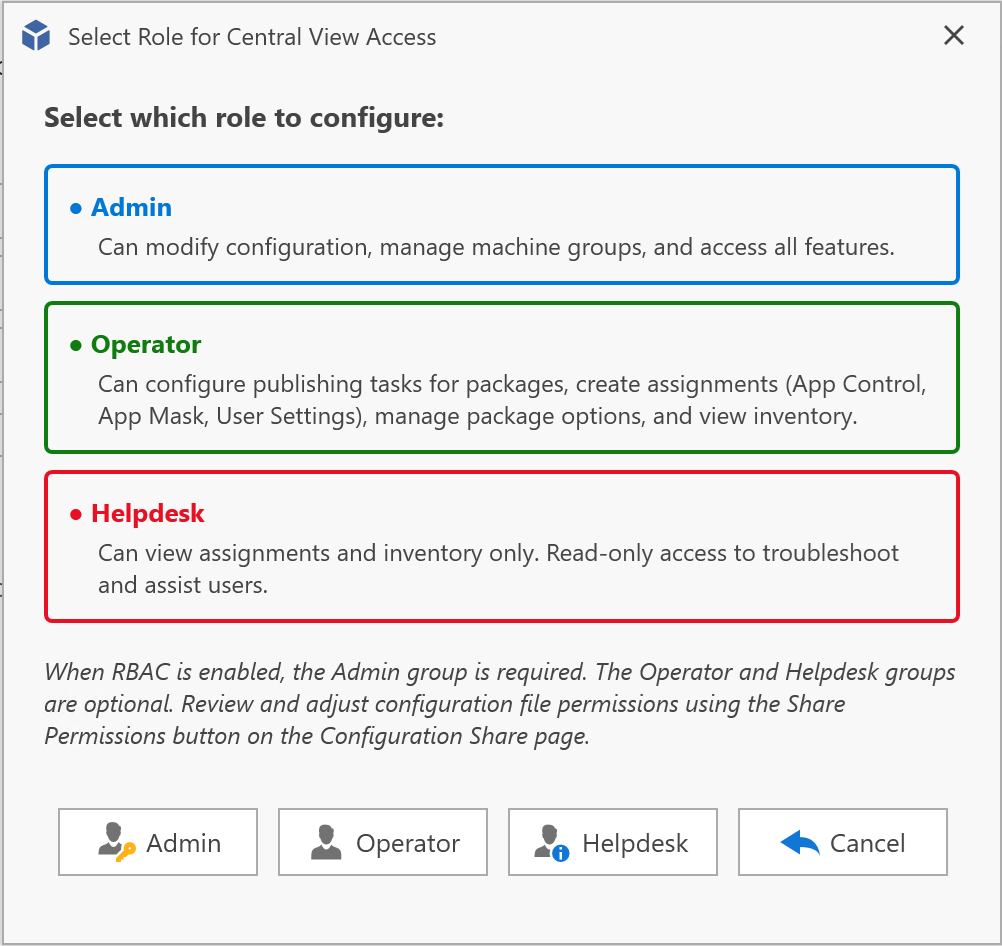
Role-Based Access Control (RBAC)
- Three configurable roles to limit access within the Central View console
- Delegate responsibilities securely and reduce administrative risk
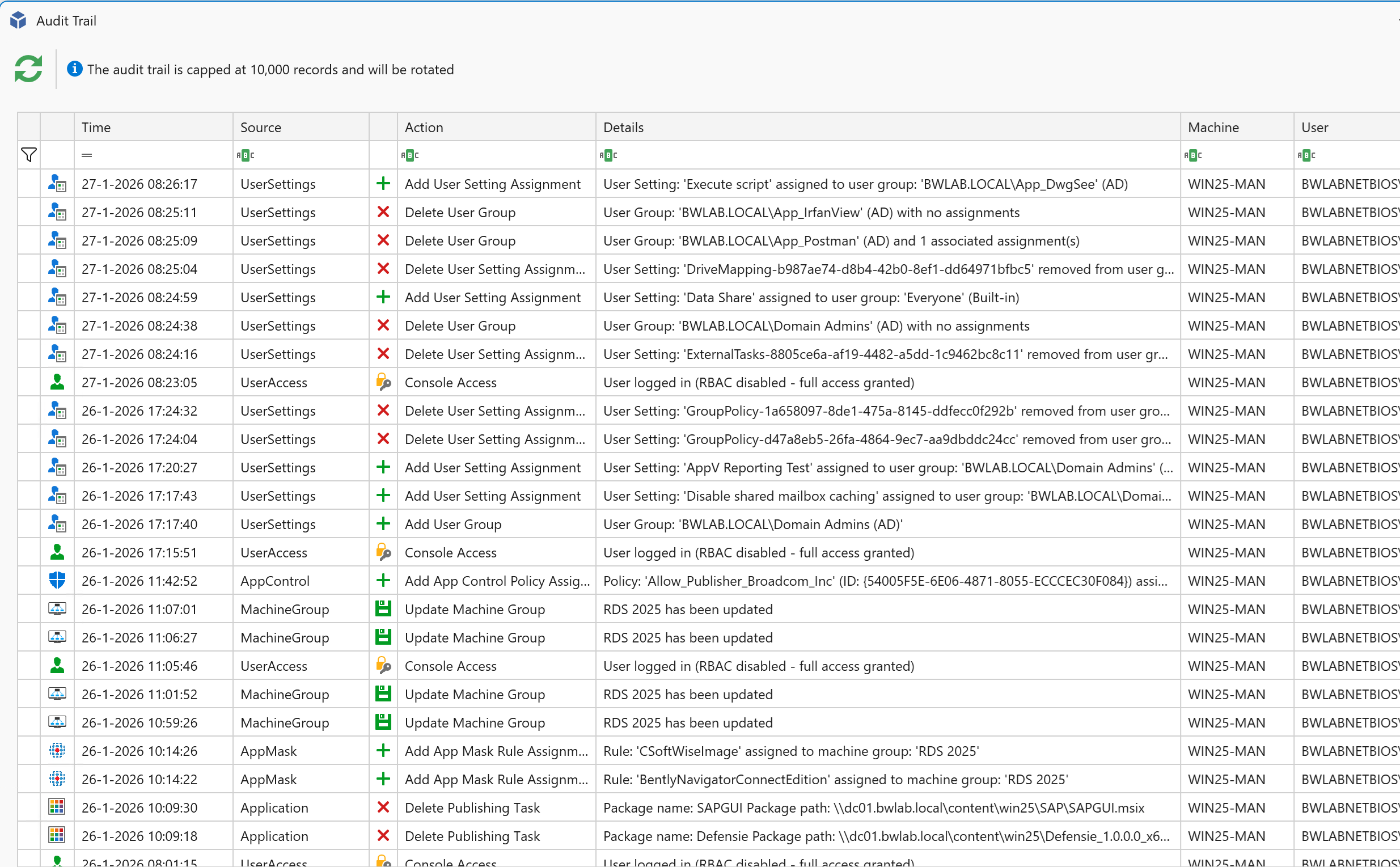
Audit Trail
- All configuration changes are logged
- Full visibility into who changed what and when
- Improved compliance and troubleshooting
Entra ID Machine Group Filter
- Filter the device inventory to display only Entra ID machines that are applicable for the selected deployment
📱 Application & Workspace Management
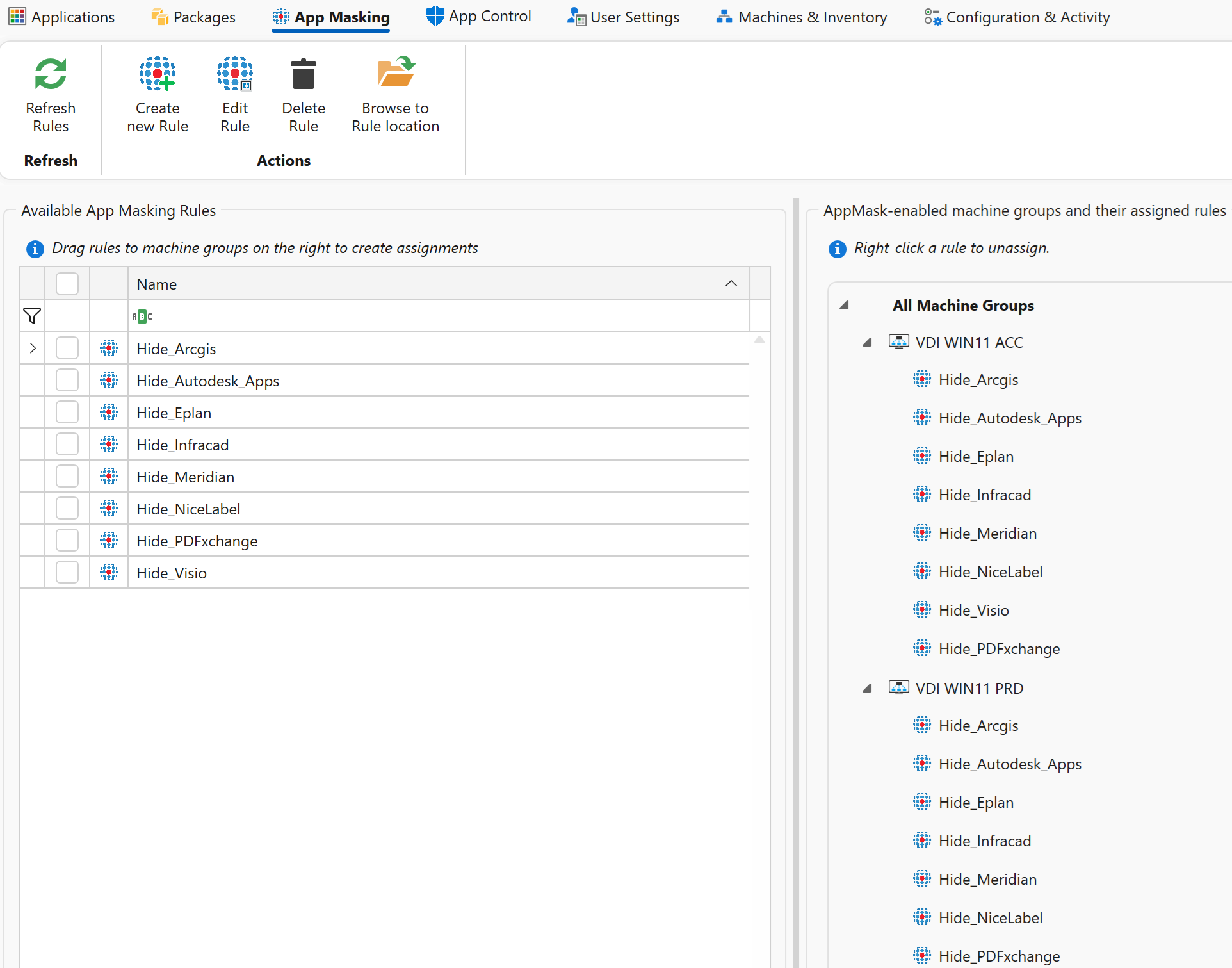
App Mask Management Enhancements
- Simplified assignment handling
- Faster and more intuitive targeting
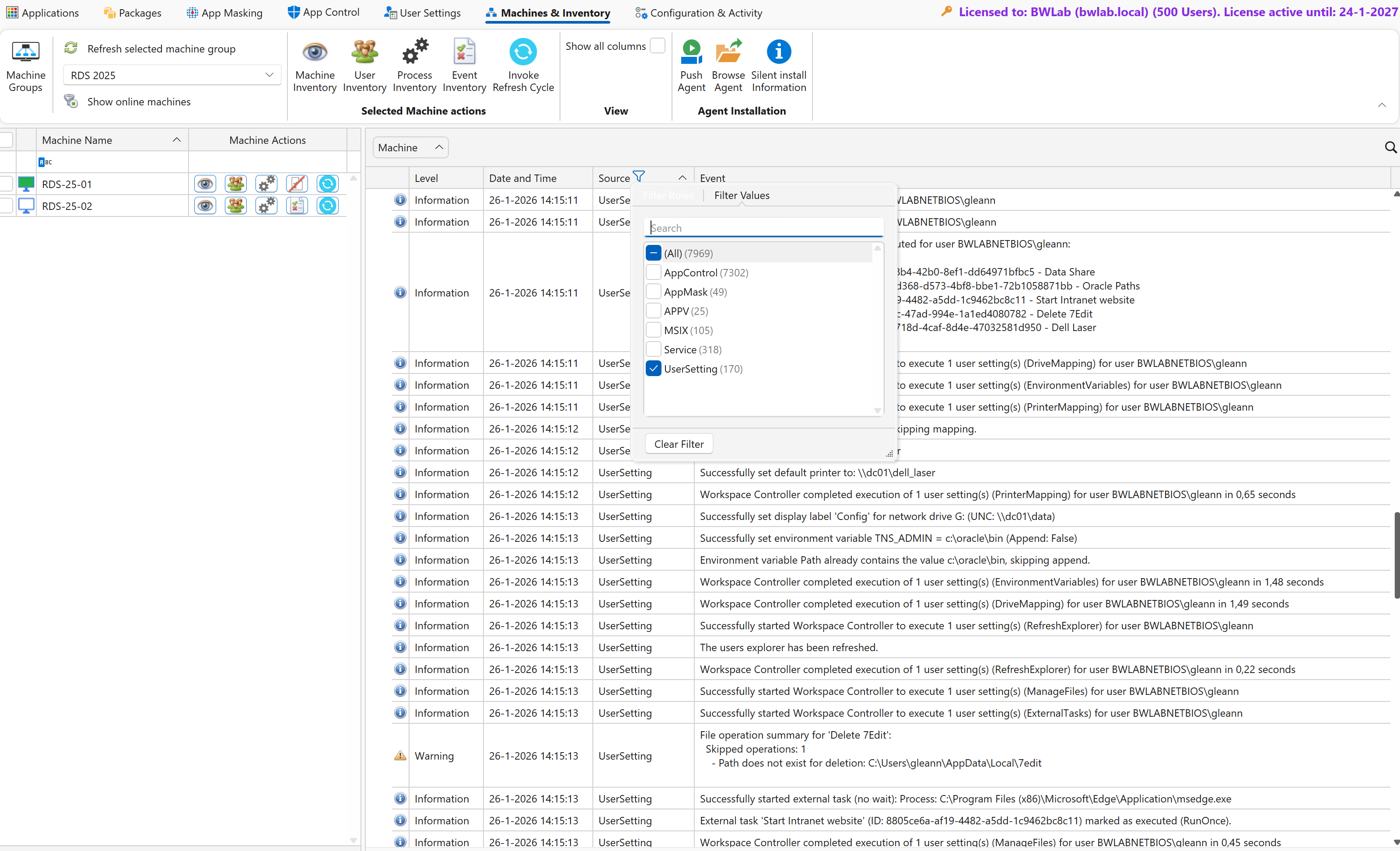
Extended Event Inventory
- More detailed operational insights for monitoring and diagnostics
QUIC File Share Support
- Secure file share access over port 443/TLS
- Improved connectivity for remote and restricted networks
Configuration Caching (Performance Boost)
- New caching mechanism dramatically improves scalability
- Supports thousands of endpoints with reduced backend load
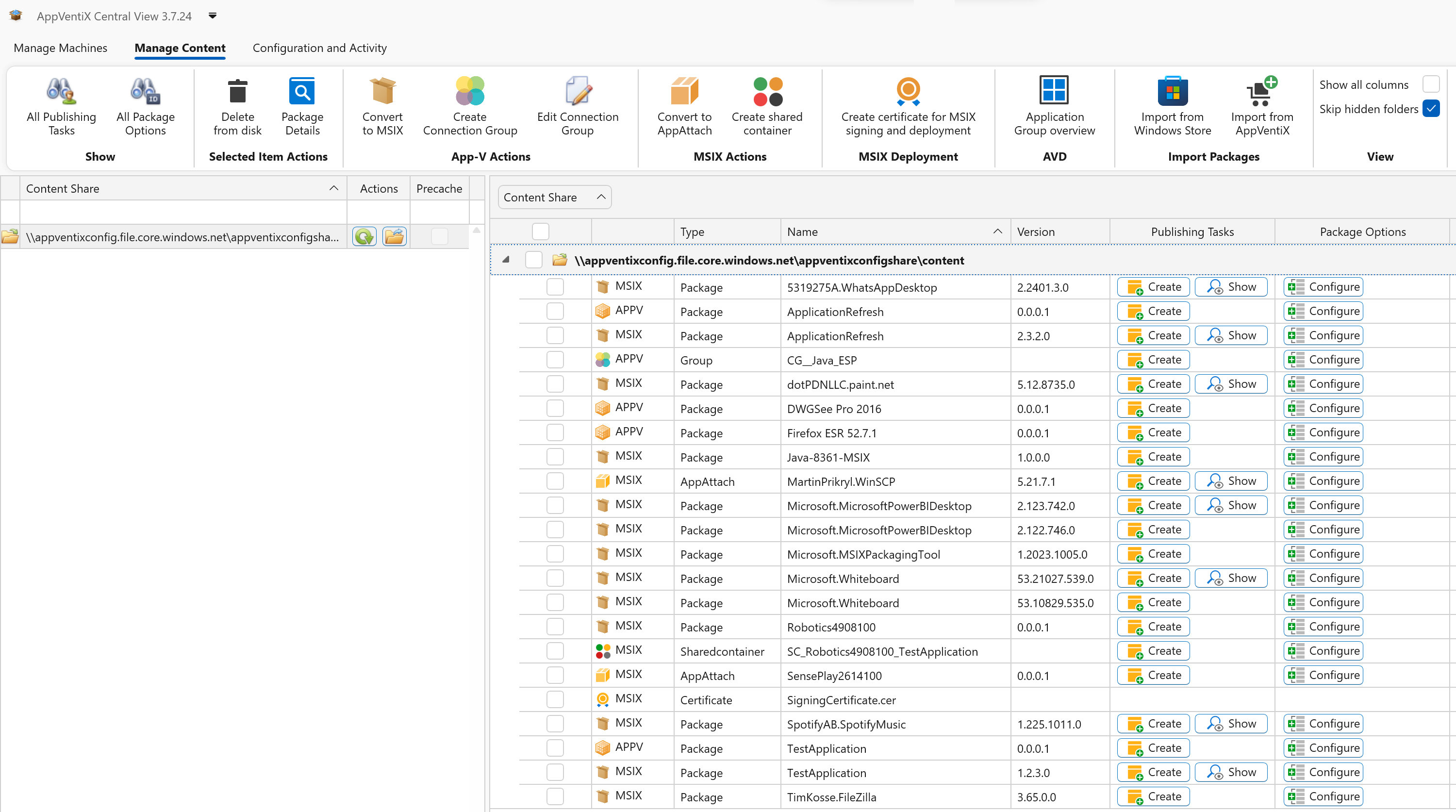
📦 Packaging & Deployment
MSIX Enhancements
- Create and manage shortcuts and file type associations during package creation
- Assign MSIX packages to all users
- View package membership in shared containers
- Prevent users from installing unmanaged MSIX packages
- New built-in registry editor
App-V Enhancements
- View package memberships and associated Connection Groups
- Improved Connection Group creation
- Enhanced deployment configuration file support
- An AppVentiX migration tool from the App-V publishing server to AppVentiX
Improved Microsoft Store Browsing and importing
- Browse the Microsoft Store directly from the AppVentiX console
- Check for updates to previously imported packages
Publishing and Filtering
- Support for assigning multiple user and machine groups within the same publishing task
Update Notifications
- Quickly publish the latest version and get notified about old versions that are published
- Simplify removal of outdated package versions
🛠️ Agent & Administration
AppVentiX Agent GUI Improvements
- Expanded functionality with enhanced management capabilities for both App-V and MSIX
- The Agent GUI can now be launched directly from the Program Files directory (no default Start Menu shortcut is created)
- Optionally publish the Agent GUI to the Start Menu using the AppVentiX Store application
- New setting to restrict the Agent GUI to administrators only, improving security and preventing unauthorized access
PowerShell Module Updates
- Enhanced cmdlets and reliability
- Improved automation and scripting capabilities
🧩 Stability & Quality
- Numerous UI and performance improvements
- General usability enhancements across the platform
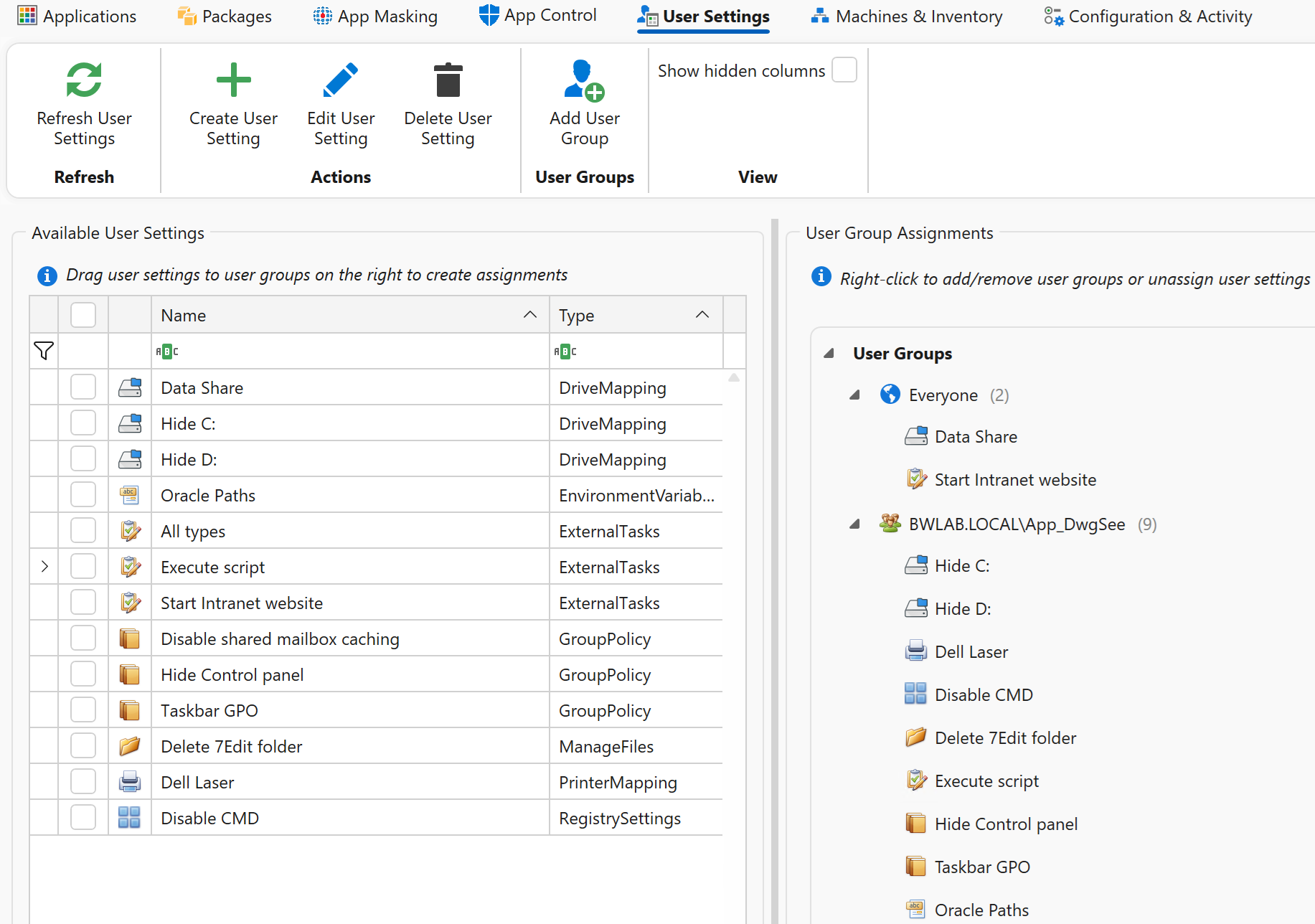
Introduction to the New Workspace Control Capabilities
Administrators can now centrally configure and deploy User Settings to fully control the user workspace without the need for complex logon scripts or multiple tools.
AppVentiX supports workspace management across on-premises (Active Directory), cloud (AVD\AWS\Windows365), and Entra ID only (laptop) environments, as well as offline and non-persistent (VDI) scenarios. All settings are managed from a single, intuitive interface, making it easy to create, edit, and assign configurations to users or devices:
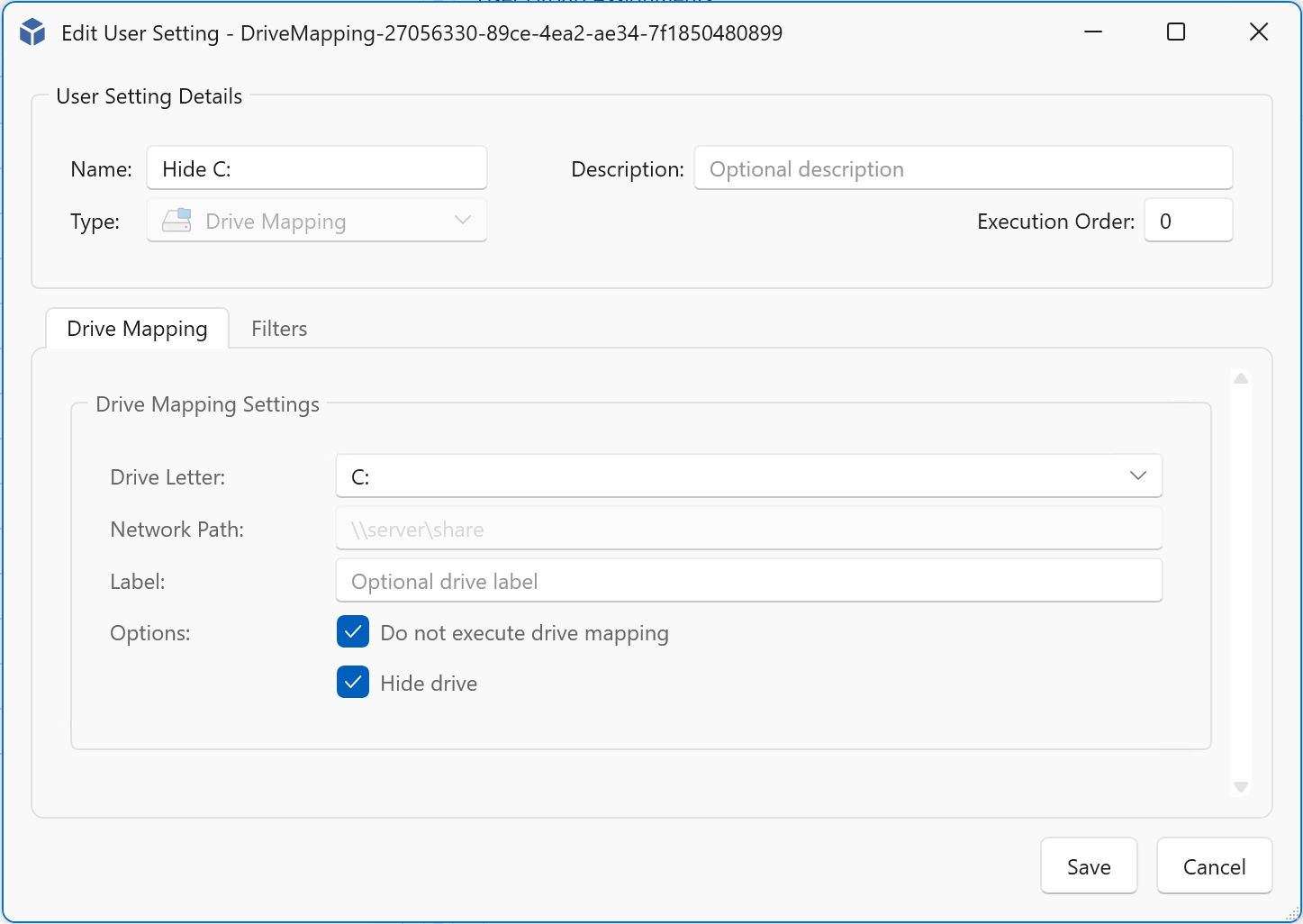
Some examples what you can do with AppVentiX Workspace Control:
- Create external tasks with an embedded script editor, no need to launch scripts from a network share:
Embedded script editor:
- Managing drive mappings and hiding drives is now easier than ever:
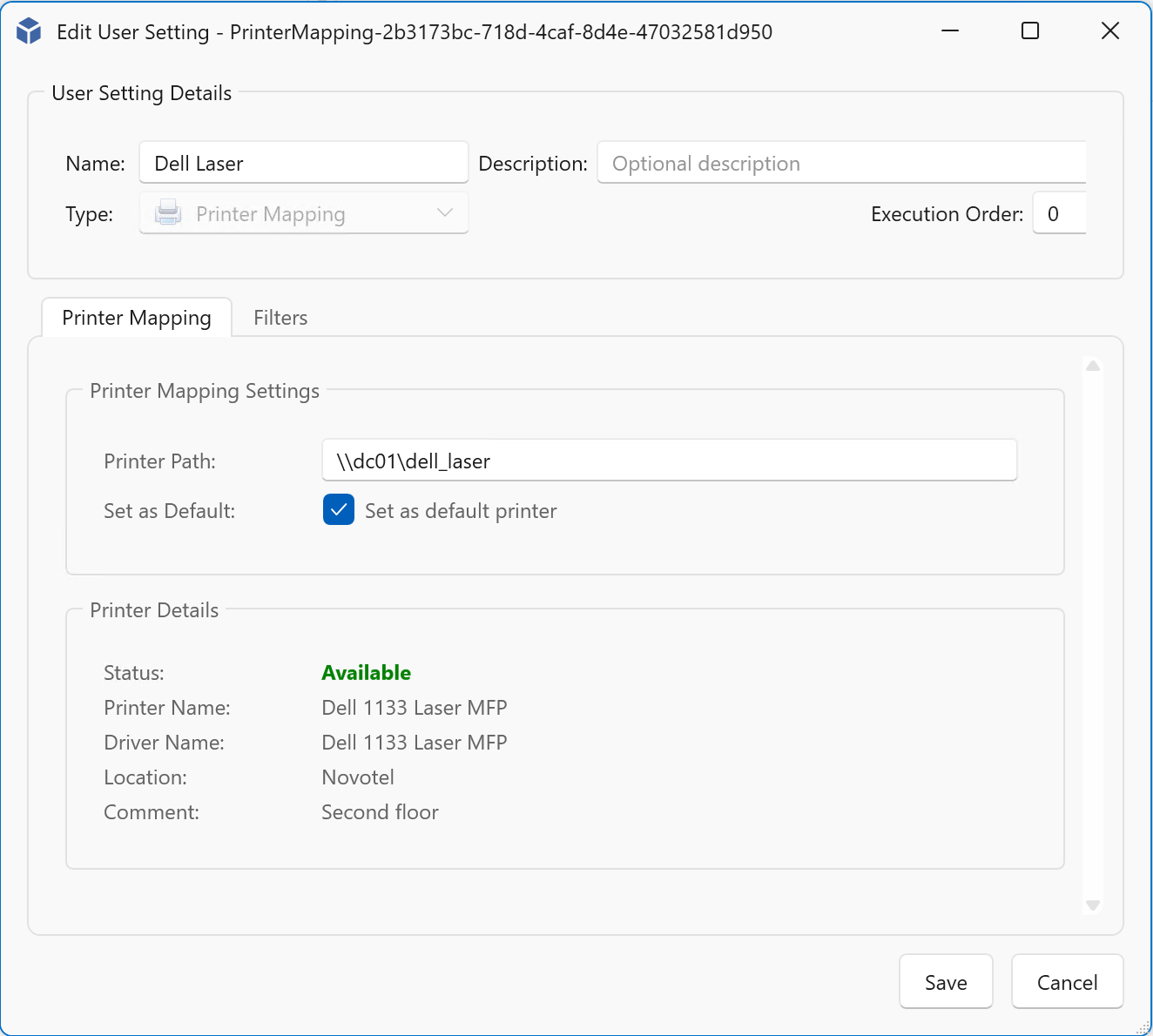
- Printer mappings can be managed in the same intuitive way:
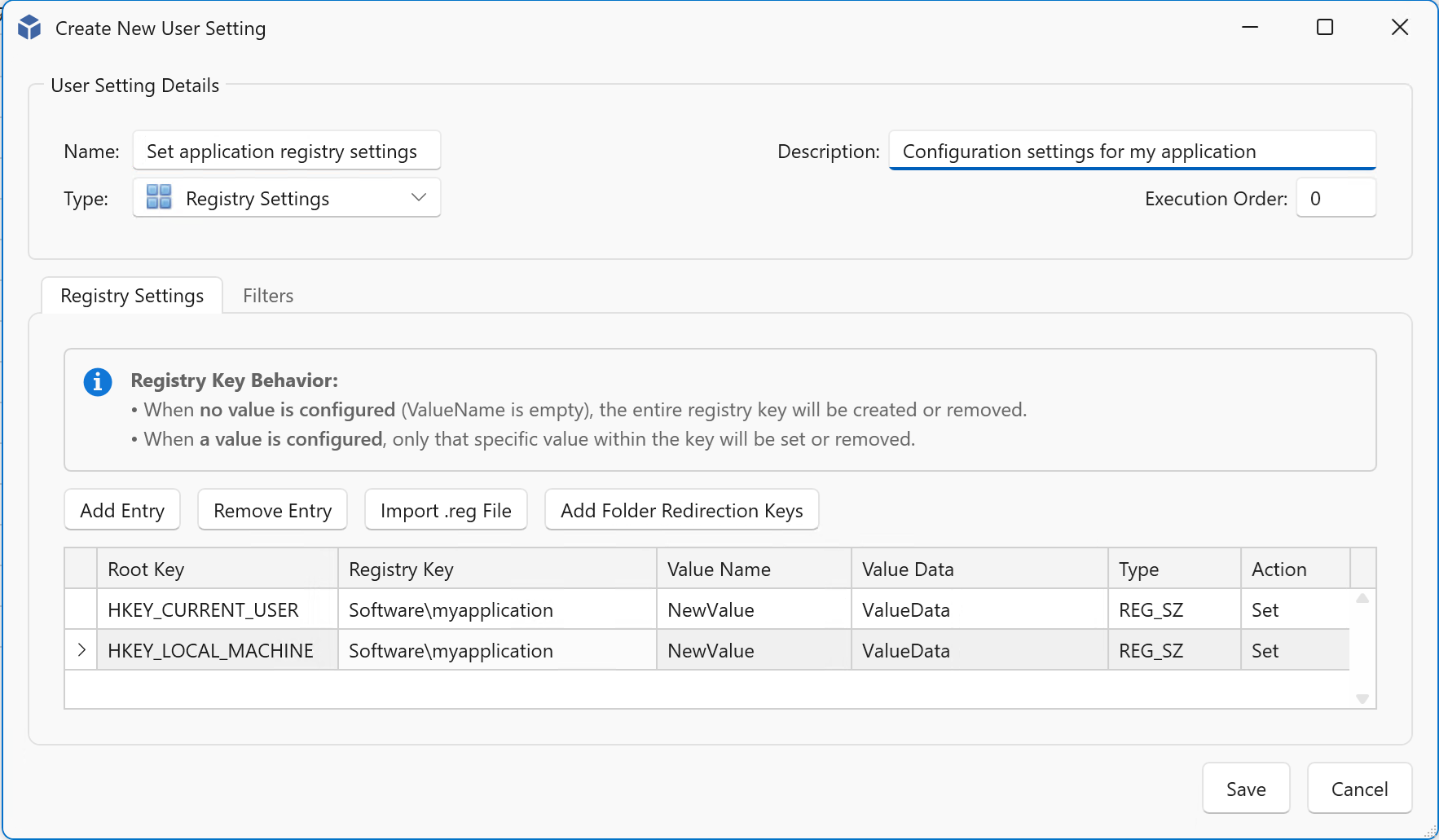
- Registry keys can easily be managed, both user and machine registry keys are supported:
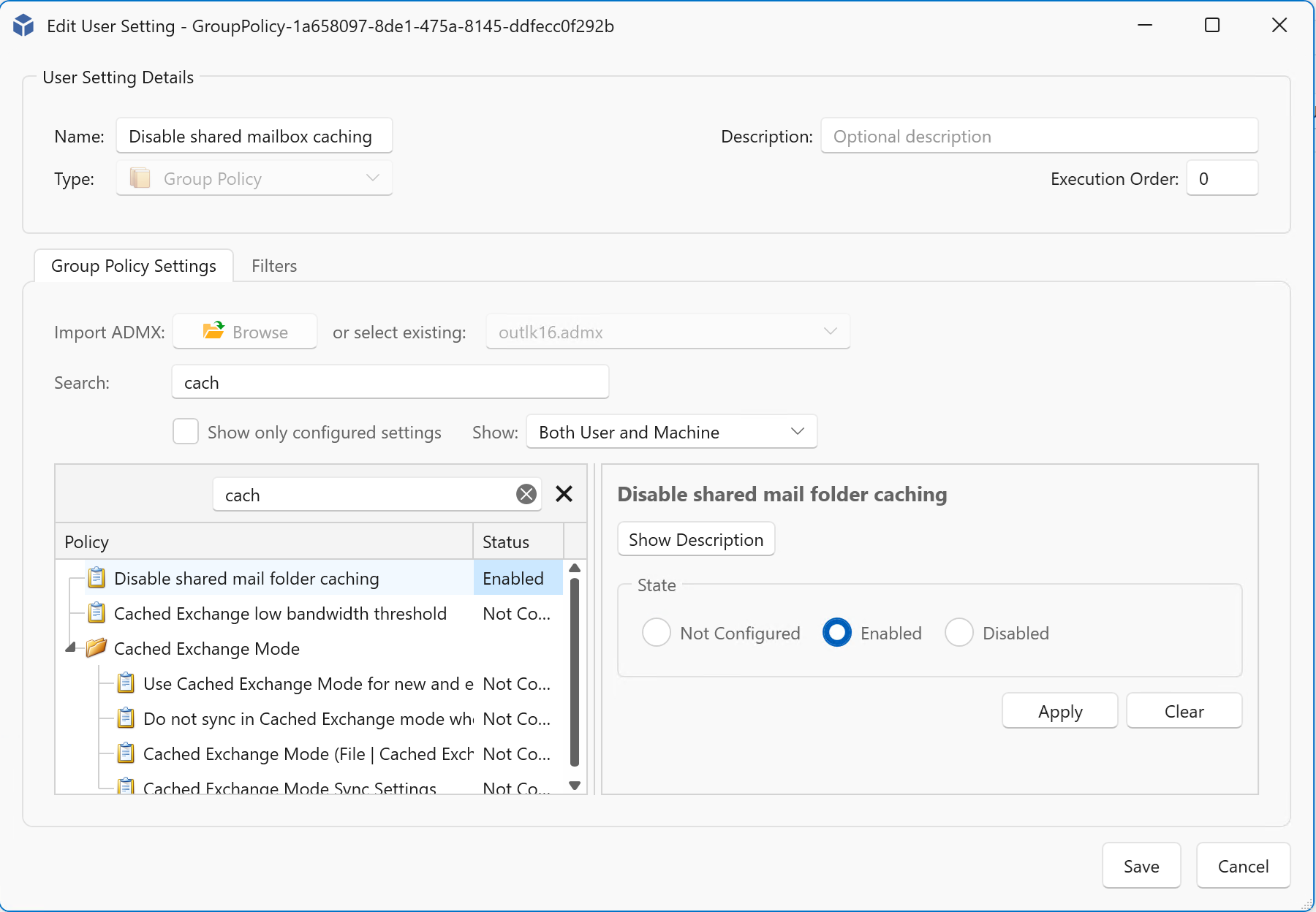
- Group policies (ADMX) can be imported, you can easily search for settings or set a checkbox to show only modified settings:
Shortcut management
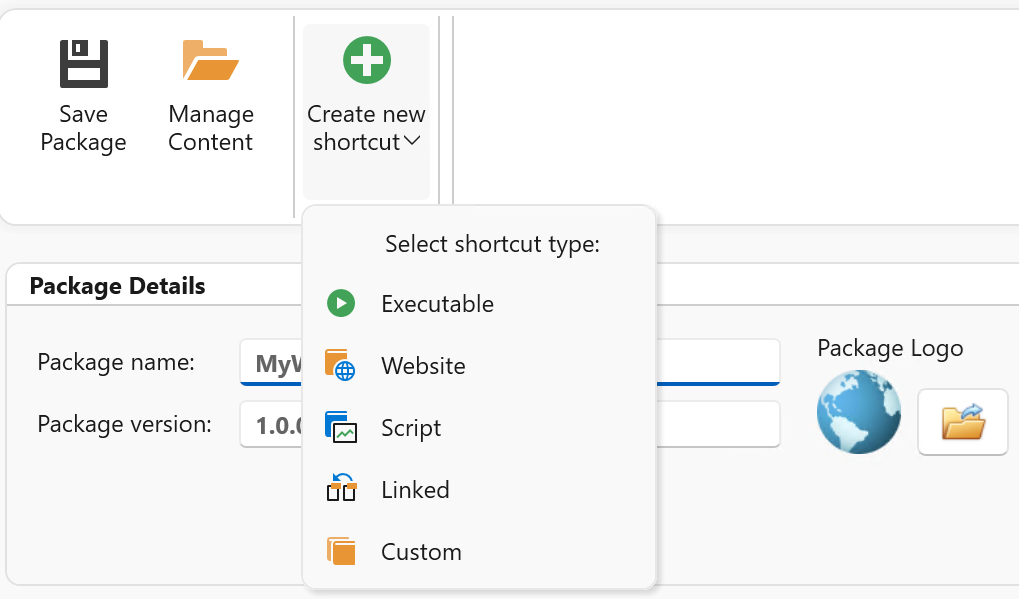
By leveraging MSIX, managing shortcuts becomes simple and flexible. You can create shortcut packages that include executables or script files, allowing you to launch any application or task.
Simply create a new package and select “Create new shortcut” to configure the target. Shortcuts can start executables with or without arguments, whether they are included inside the package or located externally on the system.
For example, you can create a shortcut that launches Microsoft Edge and automatically opens a specific website:
Result: Added to the startmenu including support for startmenu folders:
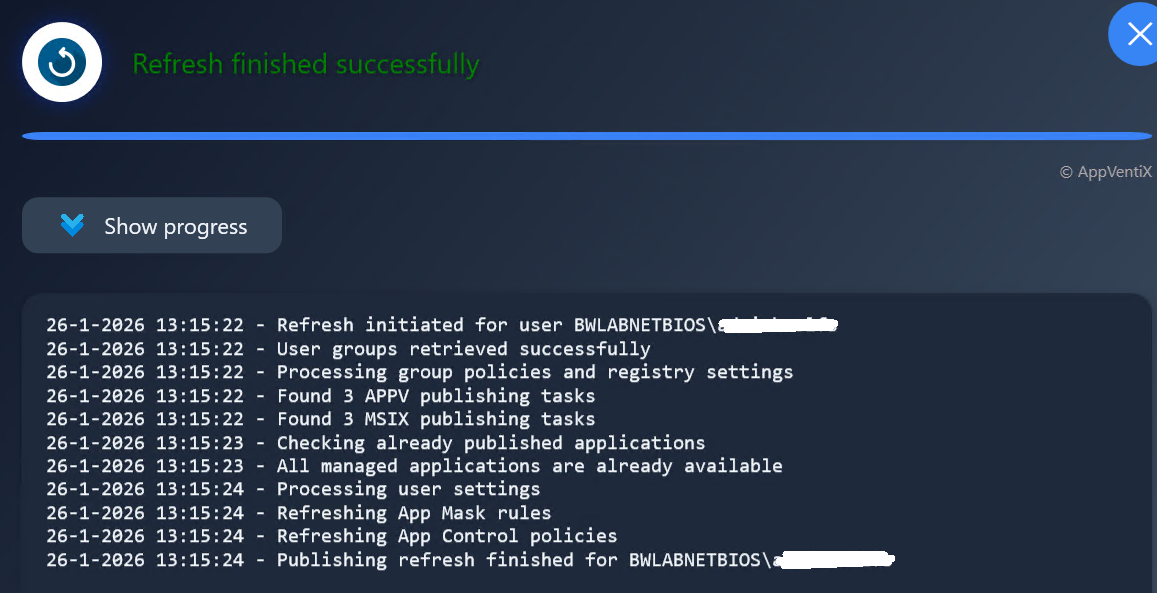
New Workspace Refresh Progress options
End users can quickly refresh their workspace and applications at any time using the new Workspace Refresh shortcut in the Start Menu, allowing changes to be applied instantly without logging off or rebooting.
This refresh updates:
- Assigned applications (App-V and MSIX)
- App Masking rules
- App Control policies
- User Settings (when configured to apply on refresh)
The Workspace Refresh shortcut in the start menu:
Optionally the Workspace refresh progress can be displayed:
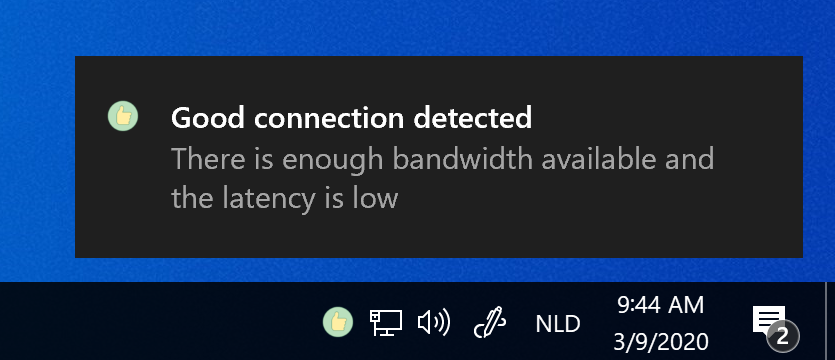
Progress Visibility at login
Also during login the progress will be displayed, this is enabled by default but can be disabled in the agent settings.
This gives users real-time feedback while:
- Applications are published
- Settings are applied
- Policies are processed
A small login progress window is displayed above the system tray, providing real-time feedback during session initialization.
Both refresh windows are localized in the following languages: English, Dutch, German & French.
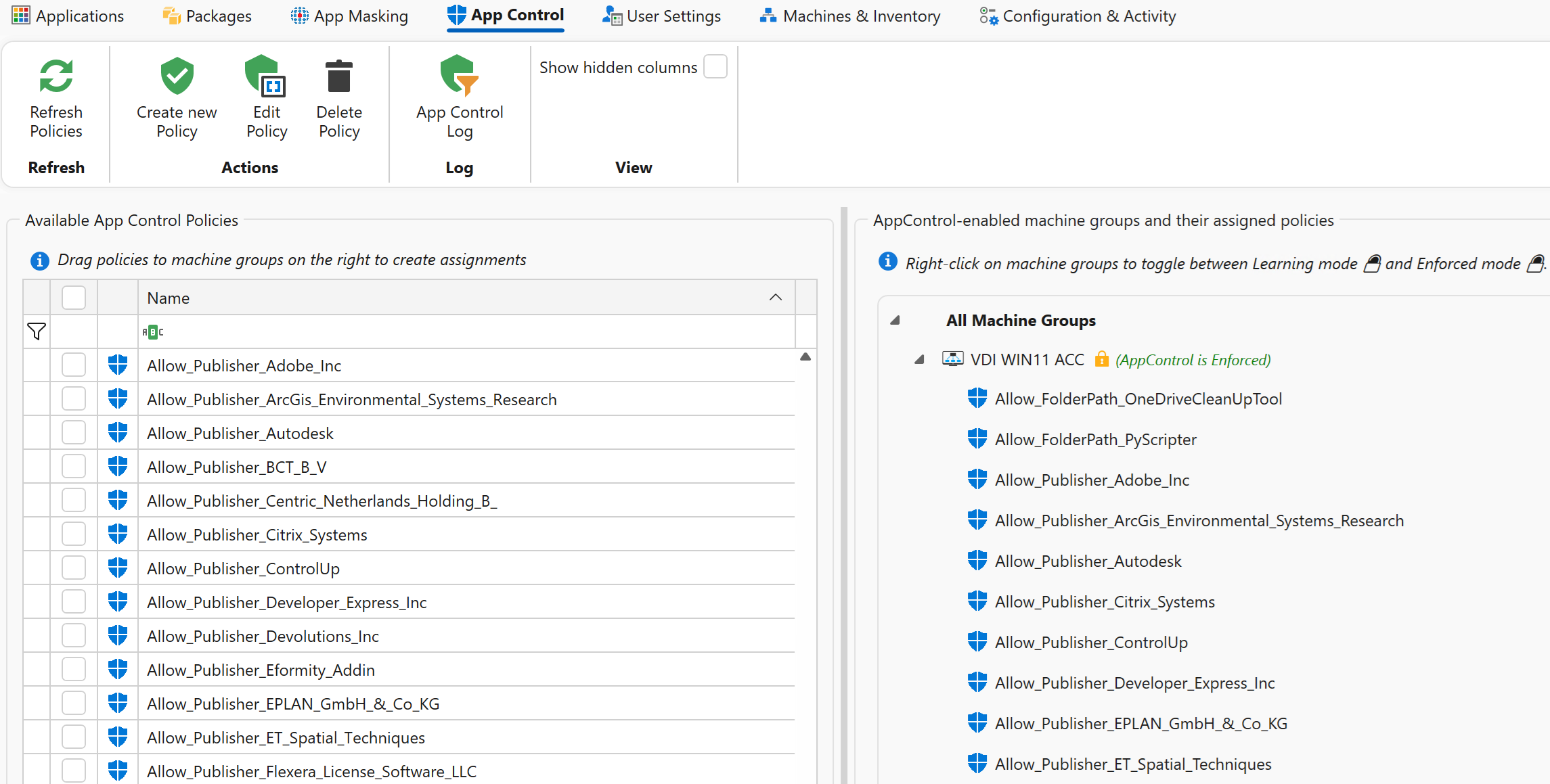
Microsoft App Control Management
AppVentiX now includes centralized management for Microsoft App Control for Business (WDAC), enabling administrators to secure endpoints while simplifying policy creation.
Key capabilities include:
- Centralized event monitoring
- Visibility into blocked processes
- Direct policy creation from captured events
- Learning mode to automatically build baseline policies
App Control policy overview and assignments:
App Control policies can be created from audit of block events or they can be created manually. All app control rule types are supported. This dramatically reduces the time and effort required to implement application control securely.
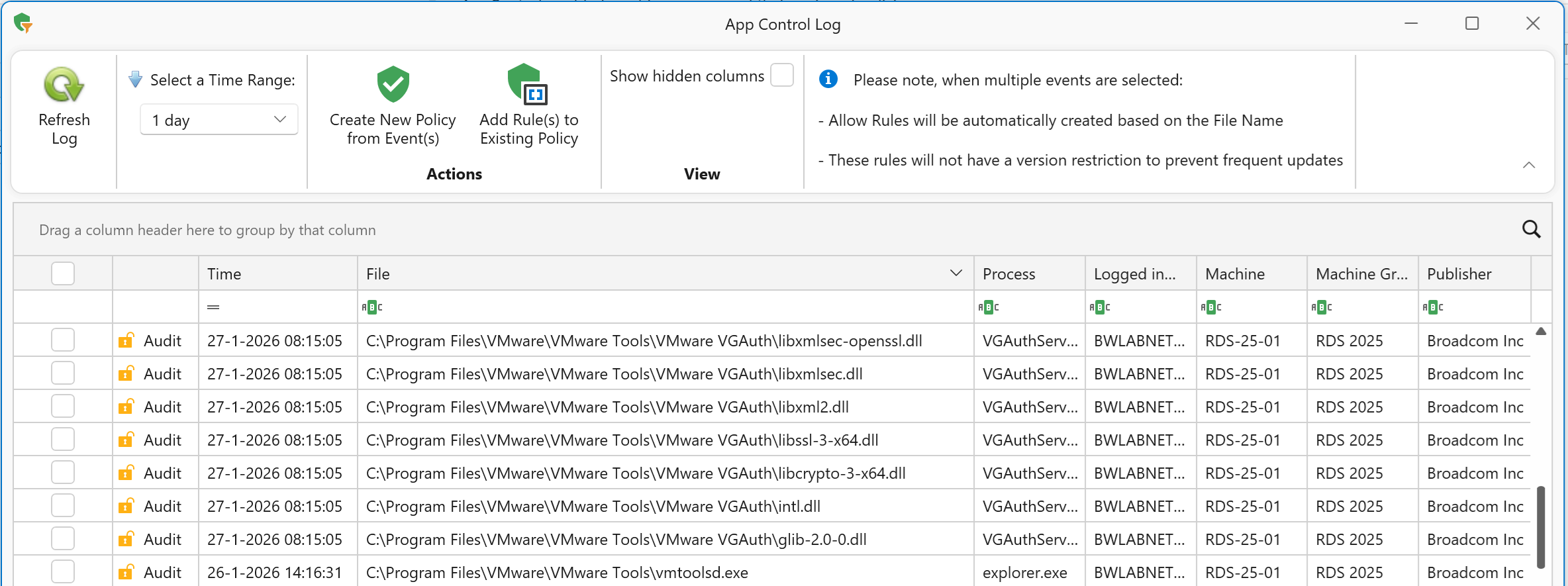
Centralized event monitoring to collect events:
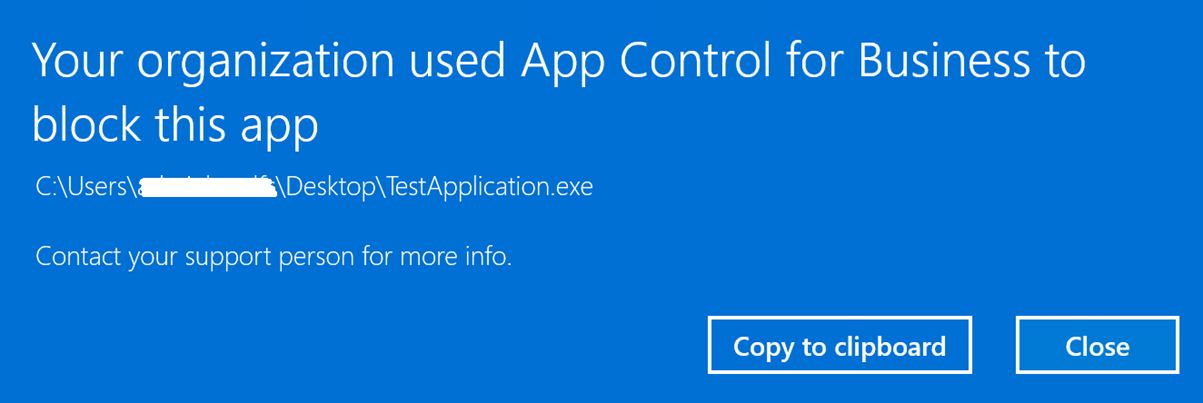
After configuring App Control in learning mode, the machine group can be switched to Enforced Mode. When a user attempts to launch an unauthorized application or process, the following notification is displayed:
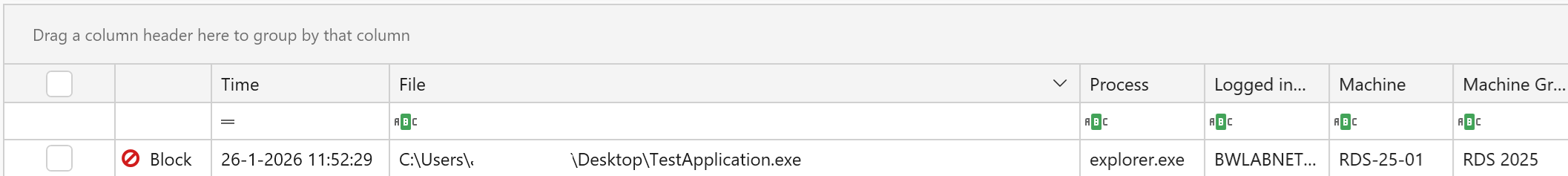
Each block event is centrally recorded for auditing and analysis. Administrators can review the event and directly create an allow policy from it. After a Workspace Refresh, the updated rule is applied immediately, enabling the application or process to run:
New RBAC roles
Role Based Access Control (RBAC) allows you to delegate access to the AppVentiX Central View console safely and efficiently.
With configurable roles, you can:
- Restrict visibility to specific areas
- Limit configuration permissions
- Assign responsibilities to helpdesk or operations teams
This ensures better governance and reduces the risk of accidental changes.
New Audit Trail
All administrative actions are now logged in a comprehensive audit trail.
You can track:
- Who made a change
- What was modified
- When the change occurred
This provides full accountability and simplifies troubleshooting and compliance reporting.
Improved FSlogix App Mask management
App Mask rules can now be assigned to machine groups with an intuitive drag-and-drop action, simplifying targeting and deployment. Additionally, rules are now stored in one location, removing the need to manage multiple content shares.
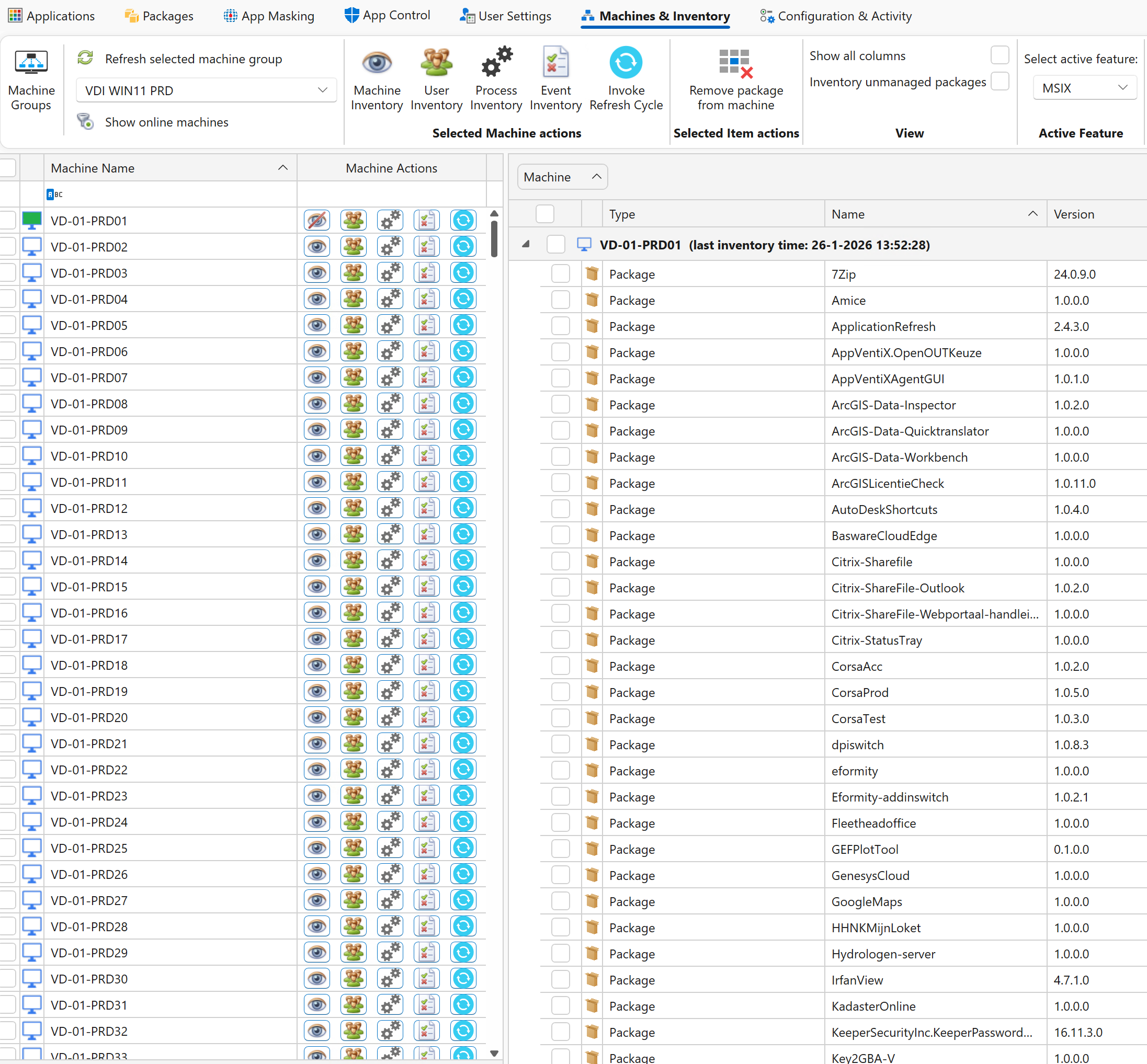
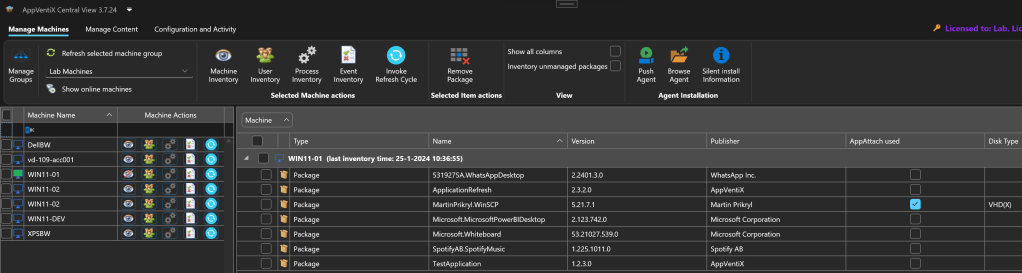
Inventory enhancements
The Machine Inventory has been enhanced with improved visibility and management capabilities, giving you a complete overview of all machines, installed packages, and versions in one centralized view.
The event inventory now includes powerful new filters, making it easy to search, isolate, and analyze events, so you can instantly get a clear picture of all applied settings and actions across your environment.
AppVentiX has a free community version and installs under 10 minutes, AppVentiX doesn’t need any back-end infrastructure. You will get immediate results which will make you confident about releasing new applications and updates in real-time. AppVentiX supports Azure Virtual Desktop (AVD), Windows 365, RDS, Omnissa and Citrix deployments both on-premises and in the cloud. Both persistent and non-persistent configurations are supported. The solution is powerful, light weight and integrates easily in your existing environment.
For more information visit the AppVentiX website: